Kaspersky Says Suspected NSA Code Was Lifted From U.S. Computer
Russian cybersecurity giant Kaspersky Lab said it uploaded mystery records connected to the National Security Agency from a private computer in the U.S., even though personnel destroyed the fabric and didn’t display it to all people outside the business enterprise. The code changed into a zippered document containing malware samples that Kaspersky’s antivirus software program removed from the house computer. The business enterprise confirmed earlier reports about its involvement in the categorized fabric leak. The program robotically uploaded the file to Kaspersky’s specialists for similar analysis.
Bad Rabbit used NSA “EternalRomance” exploit to unfold, researchers say
Despite early reviews that there has been little need for National Security Agency-developed exploits in this week’s crypto-ransomware outbreak, research launched via Cisco Talos shows that the ransomware worm referred to as “Bad Rabbit” did, in reality, use a stolen Equation Group take advantage of discovered through Shadow brokers to spread throughout sufferers’ networks. Additionally, the attackers used eternal romance and took advantage of that bypassed security over Server Message Block (SMB) file-sharing connections, permitting far-flung execution of commands on Windows customers and servers. The code intently follows an open-source Python implementation of a Windows exploit that used EternalRomance (and another Equation Group device, EternalSynergy), leveraging the same strategies revealed within the Shadow Brokers code launch.
READ MORE :
- How To Do A Clean Installation Of Windows 10
- Oracle to buy production collaboration software program maker Aconex
- Mandrake Linux founder creating Google-free Android OS
- 14 suggestions and tricks for Spotify
- The Year That Software Bugs Ate The World
Bad Rabbit, named for the Tor hidden carrier page, directs sufferers to begin with land on affected networks via a “drive-by download” assault through compromised Russian media websites. Arriving disguised as an Adobe Flash replacement, Bad Rabbit has many methods of spreading itself across networks. For example, it can use open SMB connections at the infected Windows gadget. It can also use the Windows Management Instrumentation Command-line (WMIC) scripting interface to execute code remotely on different Windows systems in the community, keeping with EndGame’s Amanda Rousseau analysis. As Rousseau and researcher Kevin Beaumont mentioned, the malware has a set of difficult-coded usernames and passwords.
But according to Talos, Bad Rabbit additionally consists of code that makes use of the eternal romance take advantage of (patched by using Microsoft in March), which makes use of an “empty” SMB transaction packet to try to push instructions into the memory of another Windows pc. In unpatched Windows 7 and later Windows running systems, the make the most can use records leakage back with the aid of the trade to decide if it is a success; on older systems, a one-of-a-kind model of the equal take advantage of is used but may crash the targeted PC’s working device inside the procedure.
Due to several similarities between Bad Rabbit and NotPetya—which includes the usage of the industrial DiskCryptor code to encrypt the victim’s hard drive and the presence of “wiper” code that could erase drives connected to the centered machine—Kaspersky Lab researchers have stated that there are “clear ties” among the two malware attacks, and other researchers have reached comparable conclusions. But there are two predominant variations: using an exclusive makes the most and the obvious targets of the assault. This time, the goals have seemingly been in general in Russia.
According to someone acquainted with the matter, Russian hackers exploited vulnerabilities within the antivirus application to breach an NSA contractor’s PC in 2015 and scouse borrow categorized files that he’d taken domestically. Israeli officials informed their U.S. Opposite numbers about the operation once they hacked into Kaspersky’s network, the New York Times reported on Oct. 11. The incident occurred in 2014, a year earlier than suggested. Russian hackers weren’t worried, consistent with Kaspersky, whose merchandise has been banned from U.S. authorities’ organizations since that September amid worries over the company’s alleged hyperlinks to Russian intelligence. Kaspersky denies it has any connection to authorities’ undercover agent corporations.
What Is a Malicious Code?
Malicious code, often called malware, is any laptop program coded intentionally to propose a surprising and unwanted event. Such applications include worms, scripts, viruses, macros, and Trojans. Trojans and worms are the most commonplace sorts of malware. Most PC structures become prone if not blanketed with the maximum present-day safety patches. Hackers treat this because of the “Happy Hour” of PC International. Unprotected packages and operating systems are smooth goals for cyberspace crook activity.
Looking further, there are other software programs/packages to be on alert for. These applications are called Unsolicited Commercial Software (UCS). UCS is an executable package that might be set up on your PC without know-how or consent. Adware is a (UCS) application that sends lots of unwanted advertisements. Spyware (UCS) will permit a hacker to observe everything you do online and ship data returned to advertising and marketing businesses or use it for self-functions to thieve your identity. It is essential to keep your PC updated with operating system patches and updates; you must also ensure the antivirus safety software program is updated. Remember to use some caution while using loose downloadable software programs. Even adware and spyware removal applications (UCS) are always bought from a reputable supplier.
Malware Code
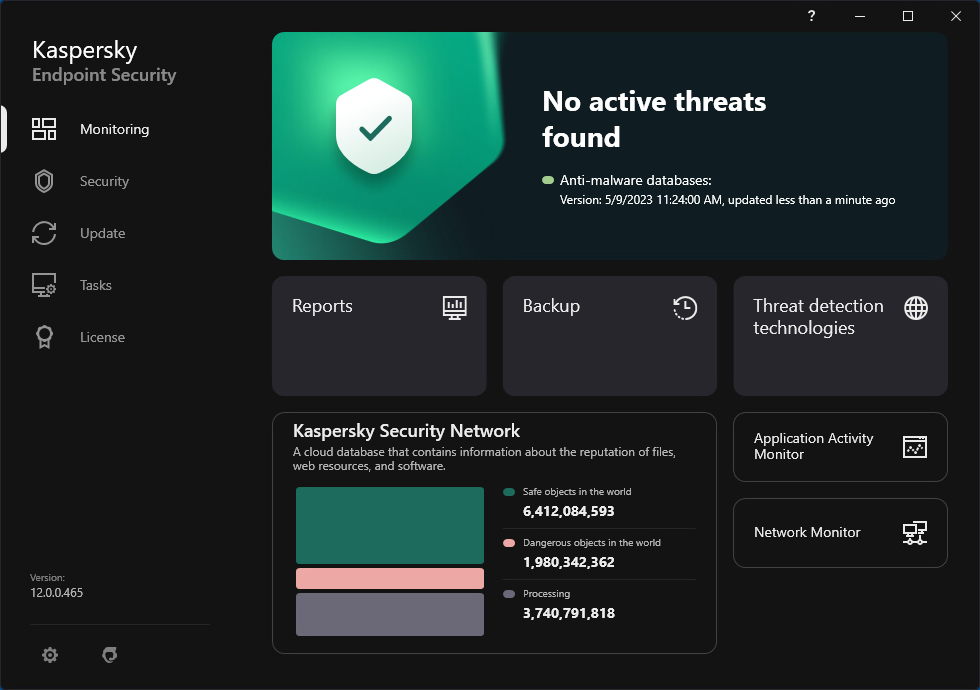
Moscow-based Kaspersky said the body of workers who tested the computer report found it contained Equation malware code, a complicated hacking toolkit linked to the NSA. They pronounced the discovery to the organization’s chief executive officer, Eugene Kaspersky, who ordered the samples deleted. The enterprise didn’t share the code with any 0.33 birthday party, consistent with the announcement. The U.S. computer user compromised the system’s security by deactivating the Kaspersky application that allows you to set up pirated software programs in keeping with the agency.
The illegal software program infected the PC with a backdoor virus, “which may additionally have allowed 0.33 events to get entry to the user’s system,” the corporation said, adding that the vulnerability becomes detected and blocked when the person reactivated Kaspersky’s antivirus. Kaspersky stated that Russian hacker viruses or other gadgets hadn’t breached its networks besides the Duqu 2.Zero. Malware in 2015. Computer specialists have linked that virus to Israel. Earlier this week, Kaspersky introduced it to offer the source code of its antivirus software for independent evaluation.




















